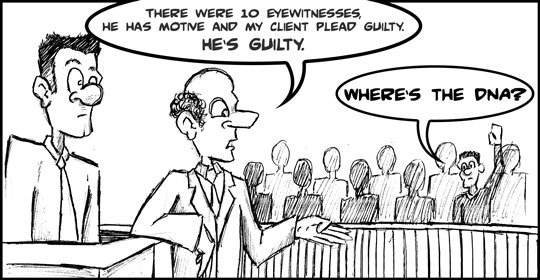
Bad forensic science: second leading cause of wrongful convictions
Bad forensic science: second leading cause of wrongful convictions
In 1985, a mistaken identification and an unreliable microscopic comparison of hair wrongly convicted Steven Avery of raping a Manitowoc woman. In 2003, Avery was…
Read more…